New credit card attack, Inter skimming kit used in homoglyph attacks

Hackers working for financial motives to extract the credit card information of the users is not new. Several methods are being adopted over the span of time to trick users into giving their details. Further progress has been made in this regard. Malwarebytes has identified a new type of attack used for credit card skimming.
It combines two techniques that are already prevalent- homographic domain and infected favicon.
How it works
Homograph Domain is a technique through which the domain name of the targeted website is spoofed. There are characters across different or the same languages that look similar and are non-distinguishable at a glance. These characters are used in creating a similar domain name, which very much looks like. It is easier to deceive a layman utilizing this trick.
The typical way to deliver the link to the target is by emailing it. This trick works most of the time, and the victim falls prey to the plan. But, as per Malwarebytes, in some instances, original websites were hacked and found injected with a code referencing an icon file.
The third-party JavaScript homogylph was then injected onto the fraudulent site. It enabled the attacker to collect the information filled up on the payment page and transfer it to the domain used for the malicious infiltration. To impose the process as authentic, the favicon was injected from the same URI as the malicious website.
How was it identified
Malwarebytes revealed that they collect information about web threats using different ways, like live crawling websites, using Virus Total tools. This attack was identified using VirusTotal. An inter-skimming kit was detected using the tool, which grabbed the researchers’ attention as it was different from the other ones. It was a .ico file instead of an HTML or JavaScript file.
The detected file was found with a gate address that made it possible to investigate it further. On further investigation, the discrepancy in the domain name came into their notice. They also observed that the original file was small and typical, while the one loaded from homogylph was large and contained a large piece of JavaScript.
The attackers were targeting more than one victim. These are the target websites that came into the notice of the researchers.
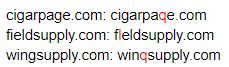
The letter in the red color is the one that was manipulated from the original website address.
The fourth domain zoplm.com which is a favicon for zopim.com, has been previously associated with Magecart group 8. Group 8 was also documented in high-profile breaches, including the MyPillow compromise. This involved injecting a malicious third-party JavaScript hosted on mypiltow.com (note the homoglyph on mypillow.com).
Mitigation
The attacker. To make successful attacks happen are employing every possible technique, even a combination of methods (as evident in this case). This has made the identification of malware hard and indetectable.
The type of attacks, like the ones mentioned above, are the ones that need awareness on the part of the users. They have to ensure that they are filling out their information on the legitimate website. They can do so by avoiding accessing the links from third party sources.




