SAP Solution Manager Vulnerability Hits With A Full-Featured Exploit Published Online
SAP Solution Manager is an enterprise software developed by the software company SAP SE (where SAP stands for Systems, Applications, and Products for data processing), to which a full-featured exploit has been published publicly online, notified by cybersecurity researchers.
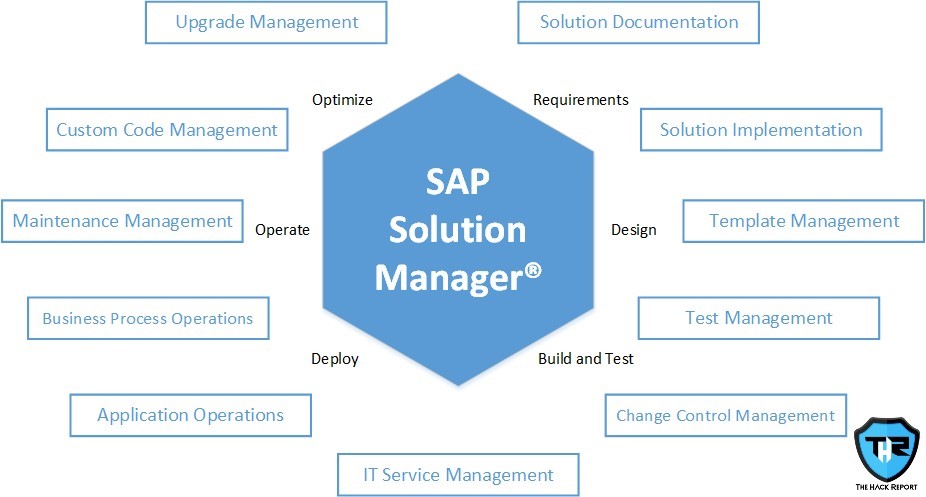
The exploit that is publicly available utilizes a vulnerability that has been registered as CVE-2020-6207 and is an absent check for authentication in the SAP Solution Manager’s variant 7.2 also called as the SolMan. SAP SolMan is an application arrangement and administration that offers start to finish application lifecycle management in widespread conditions, going about as a concentrated center for implementing and keeping up SAP frameworks, for example, ERP, CRM, HCM, SCM, BI, and others.
Analysts from Onapsis stated that “a successful exploitation could allow a remote unauthenticated attacker to execute highly privileged administrative tasks in the connected SAP SMD Agents,” alluding to the Solution Manager Diagnostics toolset used to dissect and screen SAP frameworks. The weakness, which has the most noteworthy conceivable CVSS (Common Vulnerability Scoring System) base score of 10.0, was tended to by SAP as a component of its March 2020 updates.
Misuse strategies utilizing the imperfection were later shown at the Black Hat gathering last August by Onapsis scientists Pablo Artuso and Yvan Genuer to feature conceivable assault methods that could be concocted by maverick gatherings to strike SAP servers and get root access. The severe defect which lived in SolMan’s User Experience Monitoring (previously End-client Experience Monitoring or EEM) part, accordingly putting each business framework associated with the Solution Manager in danger of a likely trade-off.
The public accessibility of a Proof-of-Concept (PoC) exploit code, consequently, leaves unpatched servers presented to various expected malevolent assaults, including closing down any SAP framework in the scene, making IT control inadequacies affecting monetary uprightness and protection, prompting administrative consistence infringements, erasing any information in the SAP frameworks, causing business interruptions, allocating superuser advantages to any current or new client, permitting those clients to run basic tasks, and perusing delicate information from the database.
Onapsis specialists explained that “While exploits are released regularly online, this hasn’t been the case for SAP vulnerabilities, for which publicly available exploits have been limited.” The arrival of a public adventure essentially builds the opportunity of an assault endeavor since it additionally grows potential aggressors not exclusively to SAP-specialists or experts, yet additionally to content youngsters or less-experienced assailants that would now be able to use public instruments as opposed to making their own.
If you like this article, follow us on Twitter, Facebook, Instagram, and Linkedin.





One Response
[…] SAP Solution Manager is an enterprise software developed by the software company SAP SE (where… The post SAP Solution Manager Vulnerability Hits With A Full-Featured Exploit Published Online appeared first on The Hack Report.The Hack ReportRead More […]