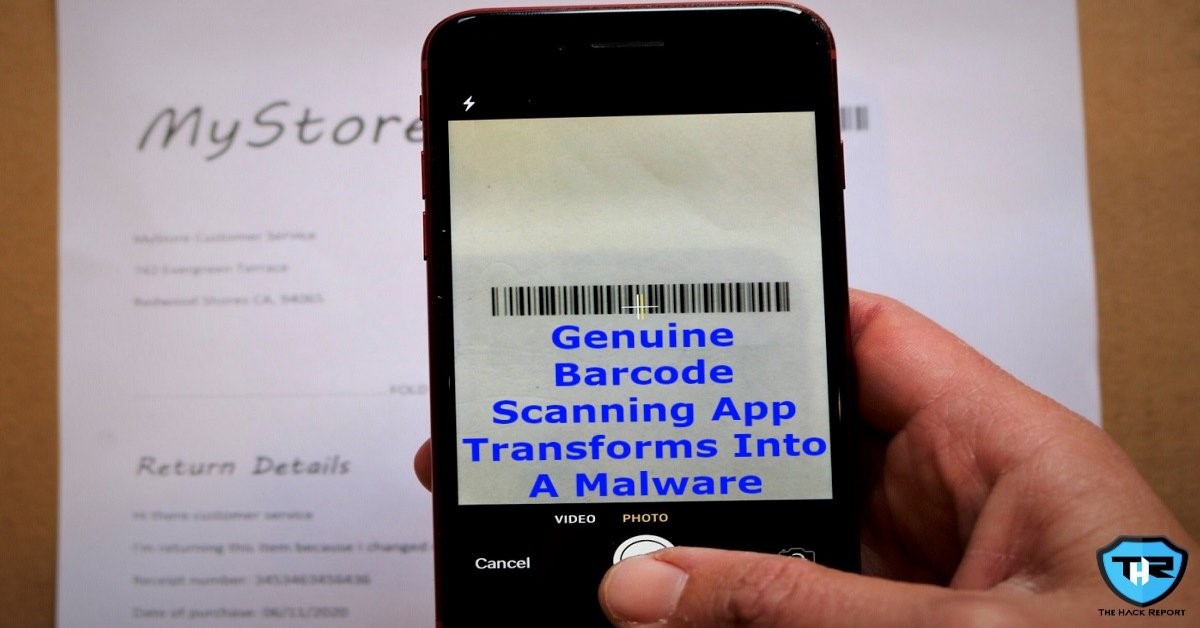
A Single Update Of Barcode Scanner App Over Google Play Store Infects Around 10 Million Users
At the end of last December, Malwarebytes began receiving distress calls from their forum patrons. Supporters were encountering advertisements that were opening through their default browsers all of a sudden from nowhere. The suspicious thing was that none of them had as of late downloaded any applications, and all the applications they had installed were downloaded and installed from the Google Play store. At that point, one of the supporters, who passes by username Anon00, found that the advertisements were launching from an application installed quite long ago, the Barcode Scanner app. This application had 10,000,000+ downloads from the Google Play Store. Malwarebytes immediately reported the detection and as a result Google immediately eliminated the application from its app store.
A significant number of the supporters had the application installed on their smartphones for extensive periods of time (one client had it installed for many years). At that point suddenly, after an update released in December, Barcode Scanner had transformed from a genuine scanner to a complete malware package. Despite the fact that Google has just removed this application, Malwarebytes predicted by observing a cached Google Play page that the update was released on 4 December 2020.
Most of the free applications on Google Play Store incorporate some sort of in-application advertising. It is done by adding an advertisement SDK to the code of the application and it is typically done towards the finish of the application’s development. Paid-for variants basically don’t come with this added advertisement SDK.
Advertisement SDKs can emerge from different third-party organizations and give a source of income for the application designer/developer. It’s a mutually beneficial arrangement for everybody as clients get a free application and the developers of the application, as well as the advertisement SDK designers, get paid.
In any case, from time to time, an advertisement SDK organization can change something on their end and these ads/promotions can begin getting somewhat forceful. Once in a while in any event, arriving the application that utilizes it in the Adware category. At the point when this occurs, it isn’t the developers of the application but the SDK organization.
In this case of Barcode Scanner, vindictive code was added which was not in past variants of the application. Moreover, the additional code utilized hefty obfuscation to avoid recognition. To check that this is from the same application designer/developer, Malwarebytes affirmed that it had been endorsed by a similar digital certificate as past clean variants. On account of its malicious aim, Malwarebytes hopped past their unique discovery class of Adware directly to Trojan, with the recognition of Android/Trojan.HiddenAds.AdQR.
The hardest event of malware investigation can be recreating what our clients are encountering. However, this wasn’t an issue with the Barcode Scanner app, it went right into it not long after being installed.
Eliminating an application from the Google Play store doesn’t really imply that it will be taken out from the infected devices. Except if Google Play Protect eliminates it afterward, it stays on the device. This is actually the thing clients are encountering with Barcode Scanner. Along these lines, until they introduce a malware scanner application or physically eliminate the application, it will keep on showing advertisements.
It is difficult to tell exactly how long Barcode Scanner had been in the Google Play store as an authentic application before it got malevolent. In light of the high number of installs and client feedback, it is speculated that it had been there for quite a long time. Unfortunately with one update, an application can turn noxious while going under the radar of Google Play Protect. It is bewildering that an application developer with a famous application would transform it into malware. Maybe this could have been the plan from the beginning, to have an application lie dormant and holding back to strike after it is popular enough.
If you like this article, follow us on Twitter, Facebook, Instagram, and LinkedIn.




