$1.3 Billion Cryptocurrency Heist Blamed On Three North Korean Hackers By US

On Wednesday, three North Korean hackers were charged by the US Department of Justice for reportedly planning to steal and extort from financial and business organizations, an amount of more than $1.3 billion in form of cryptocurrency and cash.
It is believed that three individual hackers are part of a military intelligence organization of North Korea known as the Reconnaissance General Bureau, which is also known as APT (Advanced Persistent Threat) 38, Lazarus group, or Hidden Cobra. Jon chang Hyok (31), Kim II (27), and Park Jin Hyok (36) are the three hackers charged for the incident.
Park Jin Hyok was previously charged in 2018 for being involved in the cyberattack that occurred on Sony Pictures Entertainment in 2014. He is now accused of creating and fraudulently advertising a blockchain platform and also for developing and distributing malicious applications for cryptocurrency.
The assistant attorney general of the Justice Department’s National Security Division, John C. Demers said that “North Korea’s operatives, using keyboards rather than guns, stealing digital wallets of cryptocurrency instead of sacks of cash, are the world’s leading bank robbers. The Department will continue to confront malicious nation-state cyber activity with our unique tools and work with our fellow agencies and the family of norms abiding nations to do the same.”
This incident is also being considered as a hint that the Lazarus group, to support a country through funds that have been strongly affected by economic sanctions, depends on cybertheft and such heists against various organizations and financial institutions.
This group first made its place in the sanction list of the US government in 2019 and has been considered responsible for a lot of cybercrime operations, not just in the US but abroad as well. The group is considered to be involved in the SWIFT attacks which occurred on ATM and banking networks resulting in the theft of over $1.2 billion, the ransomware outbreak of WannaCry that occurred in 2017, conducting thefts of cryptocurrency which estimates an amount of $112 million and also for conducting various phishing campaigns.
The indictment published by the US Department of Justice also highlights the plans of the hackers of 2017-18, regarding the creation of a crypto-token called Marine China. Utilizing this crypto-token users would be able to purchase stakes in shipping vessels but in actuality, it was all a fraudulent campaign for stealing funds from the government and would have involved eluding international sanctions.
The indictment also involves a scheme from hackers which included creating fake and fraudulent applications that would be advertised as genuine trading platforms of cryptocurrency while the hackers would utilize the incorporated backdoor to steal money from its user’s accounts. The backdoor has been dubbed as AppleJeus by CISA (Cybersecurity and Infrastructure Agency). CISA explained that it had discovered more than six variants of the malware, beginning in 2018. The Lazarus group utilized a combination of social engineering, social networking, and phishing methods as their initial attacking vector to manipulate users to download this malware.
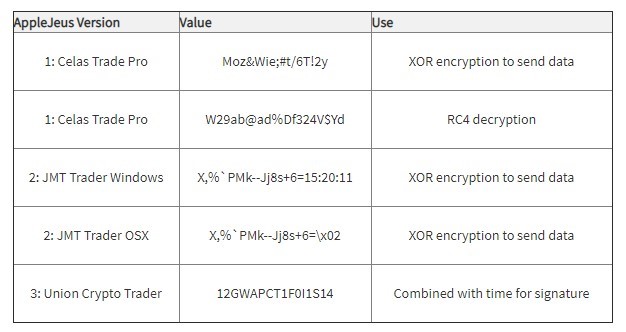
Celas Trade Pro, Kupay Wallet, WorldBit-Bot, Union Crypto Trader, iCryptoFx, Ants2Wahle, CoinGo Trade, CryptoNeuro, and Dorusio are the malicious applications that have been found by CISA. CISA explained that the AppleJeus backdoor when added targets Windows as well as MacOS operating systems and the main attention of these attacks were on sectors including finance, technology, government, telecommunication, industry, and energy.
Prosecutors from the US said that the three individuals were sent to other countries, such as Russia and China, by the North Korean government in order to develop the interests of the Kim Jon Un-lead regime in strategic and financial fields. Although it hasn’t been clarified whether the attackers from involved countries did join hands for all these cybercrime operations or not.
Warrants to seize $1.9 million of cryptocurrency, which was stored at two separate cryptocurrency exchanges, robbed from a financial service company situated in New York, were received by the US Federal Bureau of Investigation (FBI), in a related development.
It is doubtful that the accused individuals would be extradited and will be brought to trial. The individuals, Prak, Kim, and Jon are accused with a single count of conspiracy to commit bank fraud and wire fraud and another single count of conspiracy to commit computer fraud and abuse. Tracy L. Wilkison, the Acting US Attorney for the Central District of California said that “the scope of the criminal conduct by the North Korean hackers was extensive and long-running, and the range of crimes they have committed is staggering. The conduct detailed in the indictment are the acts of a criminal nation-state that has stopped at nothing to extract revenge and obtain money to prop up its regime.”
If you like this article, follow us on Twitter, Facebook, Instagram, and LinkedIn.




